A cybercrime group referred to as “GreedyBear” has been accused of stealing over $1 million by way of what researchers say is without doubt one of the most wide-reaching crypto theft operations seen in months.
Experiences from Koi Safety reveal the group is working a coordinated marketing campaign that mixes malicious browser extensions, malware, and rip-off web sites — all underneath one community.
Extensions Turned Into Pockets-Stealing Instruments
As a substitute of specializing in only one methodology, GreedyBear has mixed a number of. In keeping with Koi Safety researcher Tuval Admoni, the group has deployed greater than 650 malicious instruments in its newest push.
This marks a pointy rise from its earlier “Cunning Pockets” operation in July, which concerned 40 Firefox extensions.
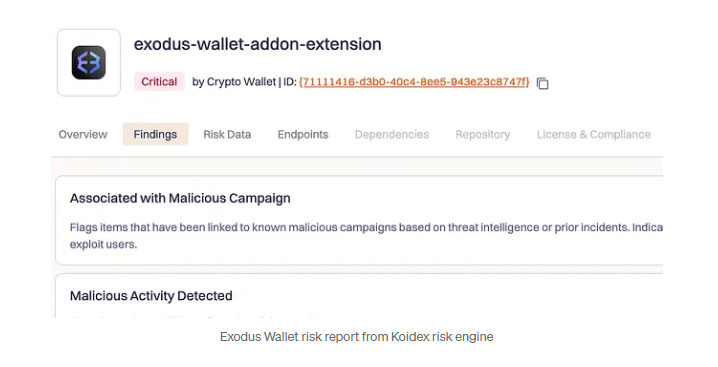
The group’s tactic, referred to as “Extension Hollowing,” begins with publishing clean-looking Firefox add-ons equivalent to video downloaders or hyperlink cleaners.
These extensions, launched underneath contemporary writer accounts, gather pretend constructive evaluations to look reliable. Later, they’re swapped for malicious variations impersonating wallets like MetaMask, TronLink, Exodus, and Rabby Pockets.
As soon as put in, they seize credentials from enter fields and ship them to GreedyBear’s management servers.

Malware Hidden In Pirated Software program
Investigators have additionally tied practically 500 malicious Home windows recordsdata to the identical group. Many of those belong to well-known malware households equivalent to LummaStealer, ransomware just like Luca Stealer, and trojans performing as loaders for different dangerous applications.
Distribution often happens by way of Russian-language web sites that host cracked or “repacked” software program. Concentrating on these looking for free software program, the attackers attain far past the crypto group.
Modular malware was additionally discovered by Koi Safety, through which operators can add or swap capabilities with out deploying utterly new recordsdata.
Pretend Crypto Companies Created To Swipe Knowledge
Based mostly on stories, along with the browser assaults and malware, GreedyBear has established fraudulent web sites that pretend themselves as real cryptocurrency options.
A few of these are mentioned to supply {hardware} wallets, and others are pretend pockets restore providers for gadgets equivalent to Trezor.
Additionally on supply are pretend pockets apps with handsome designs that trick customers into inputting restoration phrases, personal keys, and cost info.
In contrast to normal phishing websites that duplicate alternate login pages, these rip-off pages look extra like product or assist portals.
Experiences added that a few of them stay energetic and are nonetheless amassing delicate information, whereas others are on standby for future use.
Investigators discovered that almost all domains tied to those operations lead again to a single IP deal with — 185.208.156.66. This server acts because the marketing campaign’s hub, dealing with stolen credentials, coordinating ransomware exercise, and internet hosting rip-off websites.
Featured picture from Unsplash, chart from TradingView

Editorial Course of for bitcoinist is centered on delivering completely researched, correct, and unbiased content material. We uphold strict sourcing requirements, and every web page undergoes diligent assessment by our crew of high know-how consultants and seasoned editors. This course of ensures the integrity, relevance, and worth of our content material for our readers.